minimize exposure

support costs

any where, on any device

on-boarding and off-boarding

maintenance headaches
anywhere, on any type of endpoint device

Evolve IP Named Premier VMware Partner
Offers White Label Safe Harbor Program to help
businesses in a time of transition




IT is always being tasked to do more with less.
Teams need tighter security and an easy to manage infrastructure. They need predictable monthly operating expenses. They need faster onboarding. All while reducing technical debt.
That's where Desktop-as-a-Service comes in.
Eliminate the endless cycle of procuring, provisioning, maintaining, securing, and managing multiple devices.
Secure the edge and free yourself from the worry of sensitive data being compromised
Improve productivity and deliver a seamless end-user experience with 99.999% uptime
Predict the exact cost of users and remove uncertainties that come with older technologies
Work from anywhere, on any device and eliminate the need to constantly refresh hardware every few years
Simplify operations by enabling IT to add and deploy new users on Citrix, VMware and Azure within minutes vs. days/weeks
As an extension of your IT team, we deliver tailored support & consultative guidance 24x7x365 to help simplify IT
Only DaaS that Fully Integrates with UCaaS & CCaaS.



Comprehensive Suite of Cloud Solutions
We are the only DaaS Provider that Fully Integrates with UCaaS & CCaaS
-

Microsoft Teams -

Contact Center -

Cisco Webex
Microsoft Teams
Communicate and collaborate internally and externally with 99.999% uptime
- Platform level direct routing with native end-user experience
- Advanced features such as business SMS, call recording & data warehouse
- Microsoft Gold Partner with 24x7 access to Microsoft premier support

Contact Center
Leverage Evolve IP's omnichannel contact center or any third-party contact center solution to monitor staff and enhance customer experience
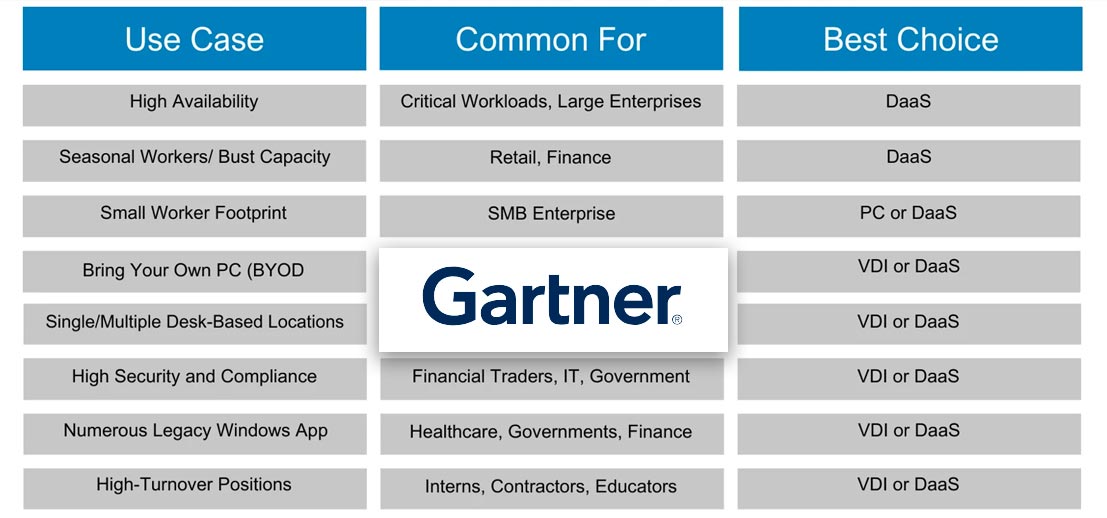
- Noted in the Gartner Magic Quadrant for 5 consecutive years
- Advanced reporting and compliant call recording
- 40+ pre-build integrations and open API

Cisco Webex
Enterprise-grade calling, messaging and meetings, all within a single app with latest features to ensure agility
- 99.999% uptime with tailored disaster recovery
- Natively integrated with contact center
- Advanced features such as business SMS, call recording and data warehouse

Ready to start a conversation?
We’re a team of trusted technology experts that work as an extension of company's IT team to help solve problems, deliver business outcomes. From the first exploratory appointment to post-implementation support, we are always available to help.
Advanced technology insights. By email.

International Law Firm Drives Communications Reliability Across 60+ Worldwide Locations and Saves Over $300,000 a Year
That’s the type of proposition I like to bring to a BOD. I can say, ‘we can get everything new, be completely redundant, it can meet all of our needs and we are going to save over $300,000 a year.’ It makes it easy for me to sell!"
– Ken Schultz CIO of Ogletree Deakins

International accounting firm increases productivity by 30% during COVID with fully integrated Work Anywhere™ solutions.
Everything was flowing, everyone's connecting...Just seamless! And everything just worked. We haven't been down since we went remote."
– Chief Information Officer, Friedman, LLP

One of the nation’s largest and fastest-growing dermatology businesses estimates savings of $6.45 Million over 5 years
Evolve IP’s digital workspaces have allowed us to acquire more practices in a faster and more profitable way. That is resulting in bottom-line cost savings and top-line business benefits."
– Jeff Francis, Vice President of IT USDP

Financial advisory firm enables employees to Work Anywhere with an integrated platform
Evolve IP’s digital workspaces have allowed us to acquire more practices in a faster and more profitable way. That is resulting in bottom-line cost savings and top-line business benefits."
– Jeff Francis, Vice President of IT USDP
We are an extension of your team with a deep bench of specialists.
We work by your side to solve problems and help you meet your business goals
Overall Net
Promoter Score
Customer Support
Satisfaction
Services NPS
Same Day Problem Resolution

LISA CARDINALE


BRADY MORRISSEY


JENNIFER PIPERATO


LAUREN CARNEVALI



LISA CARDINALE & JENNIFER GANN


JANKI PATEL & LARA HANGLEY


LAUREN COBEN

Years of Managed Cloud Experience
Global Users
Countries Serviced
Successful Cloud Migrations
Certified Experts








Simplify and future-proof your technology footprint with Evolve IP







It's nearly impossible to stay on top of every change in technology. Partner with Evolve IP and gain the combined experience of hundreds of technologists, all acting as an extension of your IT team. Helping you do more with less.